Caught On The Web
I Have A Friend In The CIA
I just got an email from “Joellen Branch”, a Technical Collection Officer, from the CIA, telling me that she will remove my name from a current child-porn case, and thus prevent my arrest, if I send her some bitcoin in the next few days.
It was sent from an email address with a .CF Domain Extension… which is the Central African Republic… so you KNOW it is legit.
They quote a Case Number, and have the CIA logo and everything… so I have NO DOUBT about its veracity!
; J
Here is the text:
Case #36925481
Distribution and storage of pornographic electronic materials involving underage children.
My name is Joellen Branch and I am a technical collection officer working for Central Intelligence Agency.
It has come to my attention that your personal details including your email address (my email was here) are listed in case #36925481.
The following details are listed in the document’s attachment:
• Your personal details,
• Home address,
• Work address,
• List of relatives and their contact information.Case #36925481 is part of a large international operation set to arrest more than 2000 individuals suspected of paedophilia in 27 countries.
The data which could be used to acquire your personal information: • Your ISP web browsing history,
• DNS queries history and connection logs,
• Deep web .onion browsing and/or connection sharing,
• Online chat-room logs,
• Social media activity log.The first arrests are scheduled for April 8, 2019.
Why am I contacting you ?
I read the documentation and I know you are a wealthy person who may be concerned about reputation.
I am one of several people who have access to those documents and I have enough security clearance to amend and remove your details from this case.
Here is my proposition.
Transfer exactly $10,000 USD (ten thousand dollars – about 2.5 BTC)
through Bitcoin network to this special bitcoin address: – REDACTED –You can transfer funds with online bitcoin exchanges such as Coinbase, Bitstamp or Coinmama.
The deadline is March 27, 2019 (I need few days to access and edit the files).
Upon confirming your transfer I will take care of all the files linked to you and you can rest assured no one will bother you.
Please do not contact me.
I will contact you and confirm only when I see the valid transfer.
Regards, Joellen Branch
Technical Collection Officer
Directorate of Science and Technology
Central Intelligence Agency
At the top of this post, my comments are tongue-in-cheek, and may come off as being too cavalier, with regards to this email.
I am now getting several of these spam, every week, in various different incarnations… some threatening me with violence for cheating or work grudges… some threaten to expose me as a child-molester… some threaten to literally expose nude pictures of me performing explicit acts.
None of these allegations… or threats… are real.
As I have stated previously, the only “real” parts of these emails, are my email address… and the scammers bitcoin account number.
EVERYTHING ELSE (the originating email address, the threat or potential threat, are all nonsense, meant to intimidate and bully the recipient into compliance.
I have posted these emails, because they are a NEW online version of the CRA Phone Scam… and (perhaps because of the lacivious nature of the “charges” leveled in the emails) the media doesn’t seem to be alerting the public to this scam as diligently, as they have previous scams.
I have no intent of paying anyone, for anything… but am posting it, in case someone else gets it, but is concerned if the threat is real, or that their reputation may be falsely maligned.
None of the threats I have posted were real.
As I have stated previously, the only “real” parts of these emails, are my email address… and the scammers bitcoin account number. EVERYTHING ELSE (the originating email address… the threat or potential threat… and the supposed law enforcement agencies involved… are all nonsense, meant to intimidate and bully the recipient into compliance.)
I have posted these emails, because they are a NEW online version of the CRA Phone Scam.
I’m not sure why… (perhaps because of the nature of the “charges” leveled in the emails?) …but, the media doesn’t seem to be alerting the public to this scam as diligently, as they have with previous incarnations.
I have no intent of paying anyone, for anything… but am posting this version, in case someone else gets it, and is concerned whether the “threat” is real.
It SHOULD be noted, that, if you have any concerns about online threats, blackmail, extortion, or threatened computer piracy, you should contact local law enforcement, and appropriate Governmental Agencies.
(For Canadian agencies, you can find links in a previous post.)
Be savvy… there are a lot of scammers and spammers out there!
Spammers And Scammers Suck – Part 3
Today I got a new version of the “Send me Bitcoin” email scam that I haven’t gotten before. This one has a different spin…
It threatens violence against me, unless I pay up.
Again, it should be stated, (as I have said in the last two blog posts,) that these emails come from a spoofed email account, and the only thing that is “real” in these emails, are my email address, and the scammer’s BitCoin account number.
Here is the scammer’s latest offering:
Hi there.
I run a site in the darknet, I sell all kinds of services – basically it is destruction to property and injury. In the main, all but the shooting. Often main reasons are rejected love or competition at work. This month she talked to me and gave me the task of empty acid in your visage. Standard order – quickly, painfully, for life.
Without too much fuss. I get money only after completing the order. Therefore, now I offer you pay me to be inactive, I propose this to nearly all the victims. If I do not see money from you, then my person will fulfill the order. If you transfer me money, in addition to my inaction, I will give you the information that I have about the client. After completing the task, I always spend the performer, so I have a choice, to get $1800 from you for information about the customer and my inaction, or to get $ 5000 from the customer, but with a high probability of losing the performer.
I’m getting payments in BitCoin, here’s my Bitcoin address – REDACTED
The summary I told above.
24 hours to decide and pay, and keep in mind that clock is ticking.
Wilbert Potter
Latest update… today I got two emails, from two different spammers.
Both made it appear that they had hacked my account, by spoofing my email. (My email isn’t hacked.)
They are getting lazy, though. Even though the instructions specify that their BitCoin accounts are case sensitive, and that I should copy and paste it, when I send them their ransom… they have pasted the document, as an image into the email, so nobody can copy and paste their BitCoin address anyway! #Geniuses
Here are the latest versions.
Click on the images below, to open ’em up, and read the (slightly) different versions.
These jerks have bought a list of emails, likely from back, years ago, when LinkedIn user information was compromised… and are spitting it out to as many folks as they can reach, hoping that some of them will be taken in by it.
I am posting the many versions, with the hope that, by posting them, I create awareness that these are spammers, and they suck… but that they should be ignored, along with the money from Nigerian Princes, and emails from the CIA.
Spammer And Scammers Suck – Part 2
So, it seems that the folks who have (at some point) hacked website databases, have data mined the breaches, and sold their email / password info to a group that is blasting the “I have nasty pictures of you” scam out to everyone.
I’ve gotten a second version of the email, threatening to release embarrassing photos/videos of me, unless I “donate” $1000 worth of bitcoins to their account.
This version was worded differently, and came to my email, with my four year old password in the subject line… so I’m guessing this was from the LinkedIn data breach.
Again, the email it came from will either be hacked, or (more likely) spoofed. The only REAL thing in the email is the Spammer’s BitCoin account.
I have no intent in paying it, and am only posting this again, because other folks might gain benefit from word of the scam getting out there, and hopefully fewer folks will be victimized.
The content of the newest version of the email, can be viewed here.
And another new version, 2 months later. It can be viewed, here.
Spammer And Scammers Suck
I remember a few years back… my Father-In-Law was one of the first folks to get the “Canada Revenue Agency” call, saying that he owed money, he was in big trouble, and they were sending a police officer to arrest him. Now it seems like everyone is getting those calls… but at the time, we jumped in our car, and drove to his house, as fast as we could, to be there, just in case… and it left us, unsettled.
Today was my turn.
I got an email, saying that I had clicked on a link that gave someone access to my webcam, and my contacts, and unless I paid $300 USD (in Bitcoin) to them, they would send embarrassing video to everyone in my contact list… and, as the owner of a business, how this embarrassment would affect my company, and brand.
As I don’t have a webcam on any of my desktop or laptop computers, I deleted the email, and went about my day.
A short time later, I thought about it some more, and realized my ipad has a forward-facing camera, and theoretically could have been compromised.
Having said that:
I’m not paying.
I don’t like extortion, I don’t like bullies, and spammers and scammers suck.
I believe it is a scam…. and several days later, there have been no further developments.
I have posted a notice, letting my friends know, that if they get an email, saying there are compromising pictures of Bob, with a link… that they should “flush” it. Clicking on, or connecting to, a questionable link is ALWAYS a bad idea… and when you KNOW it is a bad link, an even worse idea.
I have contacted the RCMP… although there is nothing to give any leads in the email. The address is either spoofed or hacked. The only valid information in the email, would be the BitCoin account number, and that isn’t trackable.
I’ll say it again… Spammers and Scammers SUCK..
If you ever get anything similar, here are the prescribed steps, according to the Canadian Anti-Fraud Centre:
If you were the victim of fraud or extortion, please contact your local police.
Additionally, there are a number of other agencies that may be able to assist.
The following list is provided as a starting point: Financial institution, credit card company, insurance company, telephone company, Provincial Consumer Protection Agency, Canadian Radio-television and Telecommunications Commission, and the Canadian Cyber Incident Response Centre.
Contacts
- Canadian Anti-Fraud Centre (http://www.antifraudcentre-centreantifraude.ca)
- RCMP Scams page (http://www.rcmp-grc.gc.ca/scams-fraudes/index-eng.htm)
- Competition Bureau (http://www.competitionbureau.gc.ca/eic/site/cb-bc.nsf/eng/h_00122.html)
- OPP fraud prevention (https://www.opp.ca/index.php?id=115&lng=en&entryid=573e164b8f94ac69670ca89a)
If you want to see the text of the email, click here.
Oh, and if you are disappointed that you DON’T get to see a picture of a naked Bob… here is as close as you will get!

Gobsmacked
I’ve never really understood the phrase “gobsmacked” until today.
I got that same old spammy direct message on Twitter, saying “Did you see this pic of you. LOL” and a link: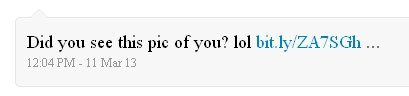
As always, I deleted the email notification, and went to the sender’s timeline.
They are a small local company, with not many followers and a pretty meager twitter feed… so as well as replying on Twitter, I took the unusual step of calling their office to let them know that they had clicked on a bad link, and they needed to change their password.
Nobody was in the office, but I left them a fairly comprehensive message, explaining (in the simplest terms possible) how they could quickly resolve their issue.
About an hour later, I got a call back, asking if I was Bob, and asking me to explain what I was talking about.
Because… you see… they PAY someone to look after their Twitter account for them. Or, more precisely, to send spam, on their behalf.
The Twitter feed that I took as someone’s sad attempt to break into the world of Social Media… was contracted out to a “professional”… who was tricked by the “Have you seen this picture of you. LOL” tweet.
And, now I understand “gobsmacked.”
I have no issue with someone helping out with Social Media. Heck, I have a number of businesses and Organizations that I help with that !!!
But I believe in value for money, and if you can’t do something properly and well… say so, and get out of the way.
Apparently not everyone feels that way… and some people are just Social Media vultures… taking advantage of small companies that don’t know any better.
Gobsmacked !!!
FYI… The Free Dictionary defines ‘gobsmacked’ as British slang, meaning astounded or astonished.
Are You REALLY LinkedIn
I am a fan of LinkedIn.
I have a number of connections, and have worked to use LinkedIn to promote and advance my business.
It is a powerful tool, and one of the premiere networks to advance your brand.
It is also “the source” of increasing frustration with the amount of email spam I receive, saying that So And So wants to connect to me, with all appearance of being a being a legitimate LinkedIn invitation… but is actually an attempt to phish (obtain my username and password surreptitiously) my account.
This has become so frequent, that I NEVER use the LinkedIn mobile app any more, and would never click on a link in a LinkedIn email, even f it appears to come from a legitimate email address.
It is a sad statement, that I now look at the source email, before I read ANY email on my Blackberry… and have had to employ a more powerful spam blocking engine,to try to stem the tide of spoofing (An email that has a legitimate address, but actually comes from a spammer) and phishing.
Certainly it is important to network, and not let the spammers stop us from connecting…. But it is equally important to make sure that our Networds are secure, but using caution, diligence, and a strong unique password.
Send Me Your Username And Password
Just got off the phone with a client who had forwarded me an email she got from the “SHAW WEBMAIL TEAM”…
Shaw.ca E-mail Notification
This message is from shaw.ca messaging center to all shaw.ca email account owners.
We are removing access to all our mail clients. Your email account will be upgraded to a new enhanced web mail user interface provided by shaw.ca.
Effective from the moment this email has been received and response received from you. shaw.ca will discontinue the use of our shaw.ca mail and our shaw.ca mail Lite interfaces.
To ensure your e-mail address book is saved in our database.
Please click the reply button and enter your shaw.ca
username here ( )
Password here ( )
City ( )
Country of Residence ( )
And send it back to us, which will enable us to transfer your contacts to our new Web mail client database.
All e-mails will be safe in this transition! All your old email will still be there and you will have new unread messages waiting for you.
We are confident that you will like the new and improved web mail interface.
Failure to comply with this notice immediately will remove your access from our shaw.ca database.
Thank you for using shaw.ca.
Yours Sincerely,
Shaw.ca Web-mail Services
I confirmed with my client that she should NEVER email her info to Shaw (or anyone else) who asks for it.
Shaw already HAS it, and wouldn’t need you to send it to them again.

(As a further tip off, the email reply address is in China… although a more professional hacker would be able to tweak that…)
But I just thought I would quickly write this, as a reminder, that you should NEVER give your password to ANYONE !!!
My wife would ask me to add: Not even to your spouse… (because they will mess with your Facebook and Twitter accounts)
Happy May Day !
PS I contacted Shaw Cable and they became aware of this, first on Sunday.



